Today I started playing with Windows Azure Access Control Service (ACS) and ran into some issues while making a simple application based on the guide here: http://www.windowsazure.com/en-us/develop/net/how-to-guides/access-control/. I had to search for a number of things on the Internet to finally get it working so I thought I would write a simple blog post which kind of summarizes the issues and how to resolve them.
The problems I ran into were because the guide was focused on Windows 7/Visual Studio 2010 and I was using Windows 8/Visual Studio 2012.
It may very well be documented somewhere but I could not find them and there may be many “newbies” like me who are just starting out with ACS on Windows 8/VS 2012 and hopefully this blog post will save some time and frustration implementing this ridiculously easy and useful technology for implementing authentication in their web applications.
With this thought, let’s start 🙂
Windows Identity Foundation Setup
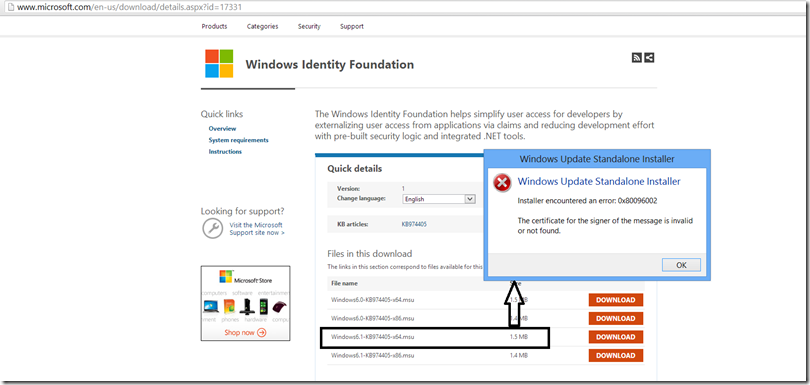
When I downloaded and tried to run the “Windows Identity Foundation” from “Windows Identity Foundation” link from above, I got the following message:
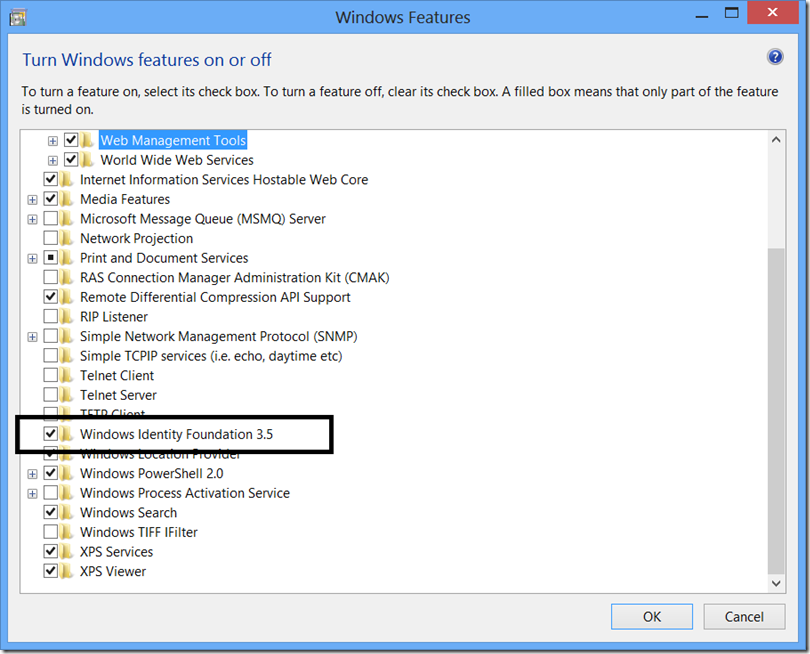
I found the solution for this problem on Windows 8 Community Forums: http://answers.microsoft.com/en-us/windows/forum/windows_8-windows_install/error-when-installing-windows-identity-foundation/6e4c65a5-ea24-431c-b4f0-b8740e97cf46?auth=1. Basically, the solution is that you have to enable WIF through “Turn Windows Feature On/Off” functionality. To do so, go to Control Panel –> Programs and Features –> Turn Windows Feature on or off.
Also once WIF is installed, I was able to install Windows Identity Foundation SDK. Prior to that I was not able to do that as well.
Dude, Where’s My “Add STS Reference” Option!
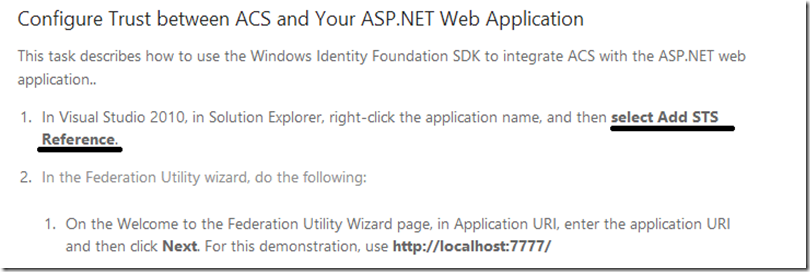
OK, moving on. After following some more steps to a “T”, I ran into the following set of instructions:
So I followed step 1 but could not find “Add STS Reference” option when I right clicked on the solution in Visual Studio. Back to searching and I found a couple of blog posts:
http://blogs.infosupport.com/equivalent-to-add-sts-reference-for-vs-2012/
http://www.stratospher.es/blog/post/add-sts-reference-missing-in-visual-studio-2012-rc
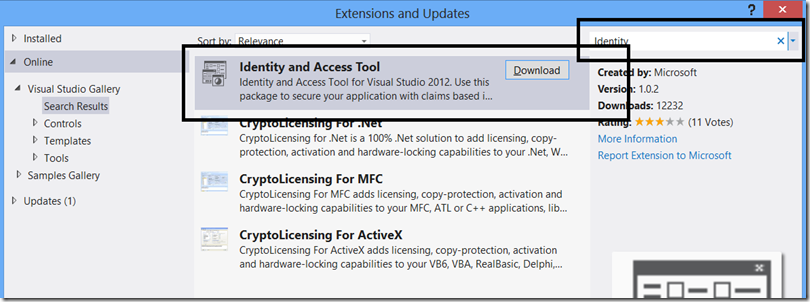
Basically what I needed to do was install “Identity and Access Tool” extension. To do so, just click on Tools –> Extensions and Updates… and search for “Identity” as shown below:
One I installed it, I was a happy camper again 🙂
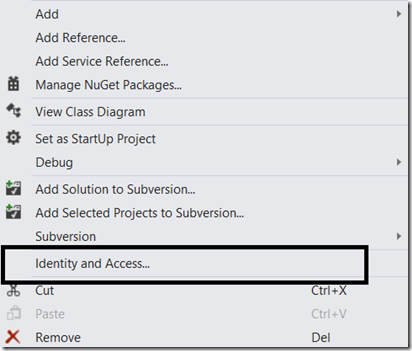
And instead of “Add STS Reference” the options’ name is “Identity and Access” 🙂
Configuring Trust between ACS and ASP.NET Web Application
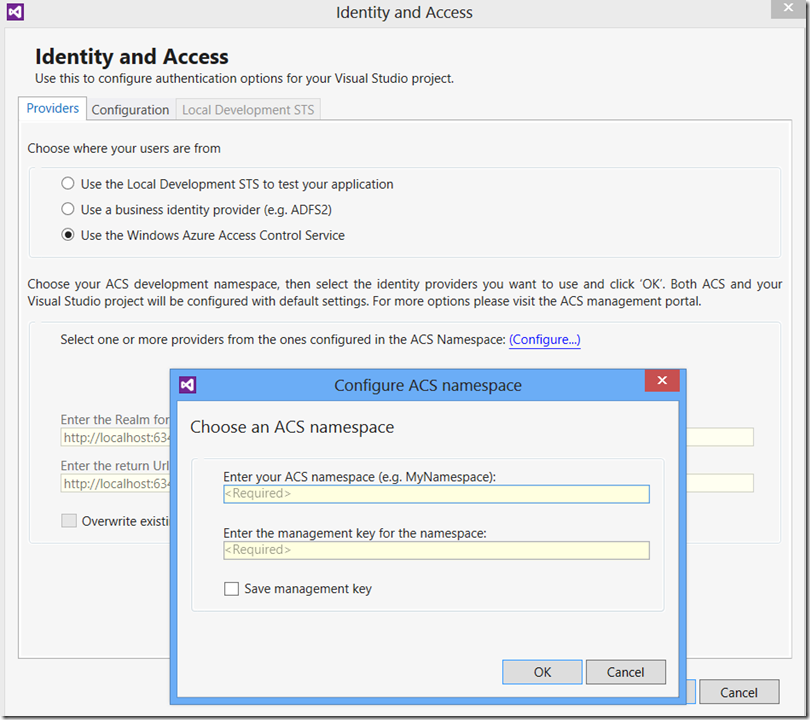
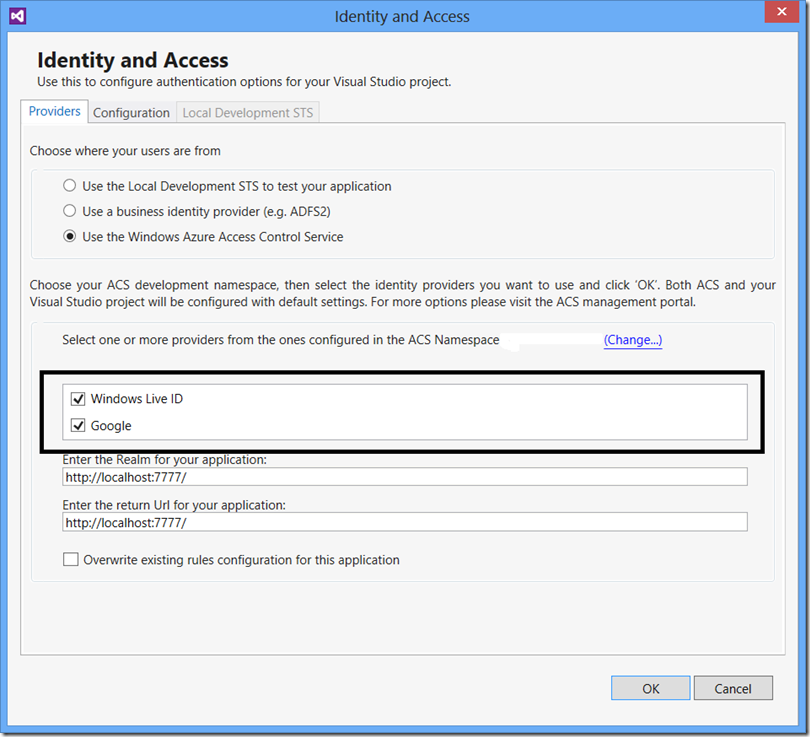
Next step is configuring trust between ACS and ASP.Net Web Application. The steps provided in the guide were for Visual Studio 2010 and clicking on “Identity and Access…” gave me an entirely different window.
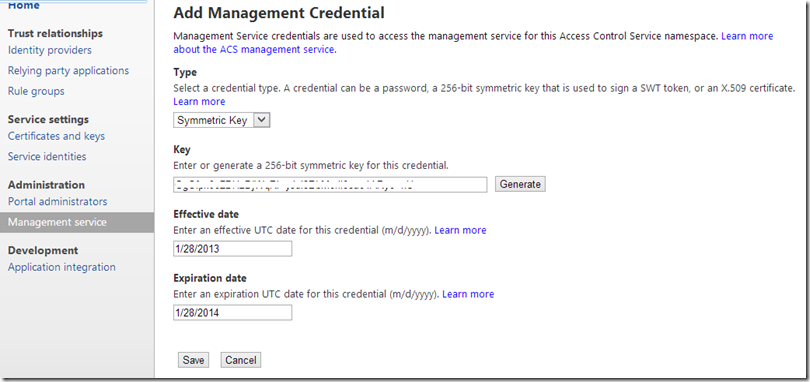
Again this blog post from Haishi Bai came to my rescue: http://haishibai.blogspot.in/2012/08/windows-azure-web-site-targeting-net.html. However one thing that was not clear to me (or consider this my complete ignorance :)) is from where I’ll get the management key. I logged into the ACS portal (https://<yourservicenamespace>.accesscontrol.windows.net) and first thought I would find the key under “Certificates and keys” section there (without reading much above. You can understand, I was desperate :)). I copied the key from there and entered that key in the window above but that didn’t work.
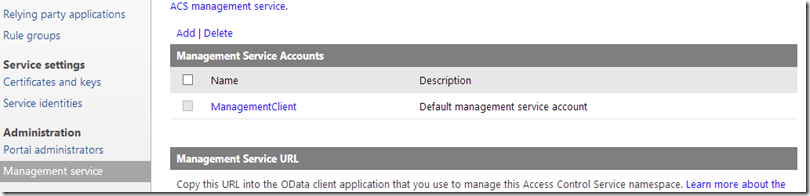
As I looked around, I found the “Management service” section under “Administration” section and tried to use the key from there.
Clicked on “Generate” button to create a key and used it and voila it worked :). The portal also generates a key for you which you can also use, BTW.
Running The Application
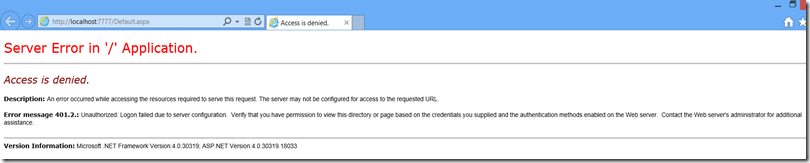
Assuming the worst part was over, I followed remaining steps in the guide and pressed “F5” to run the application. But the application didn’t run :(. Instead I got this error:
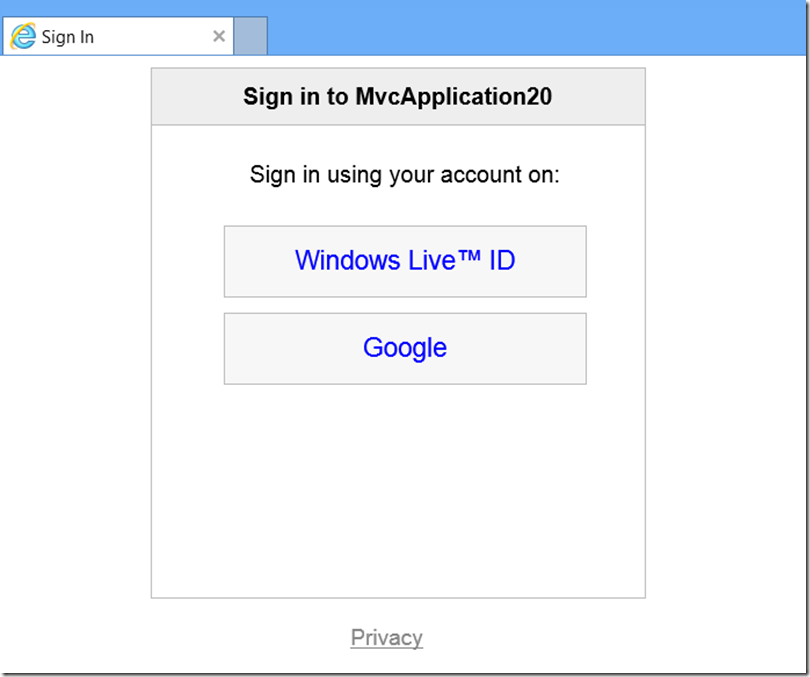
Again I was at the mercy of search engines :). I searched for it and found a blog post by Sandrino: http://sandrinodimattia.net/blog/posts/azure-appfabric-acs-unauthorized-logon-failed-due-to-server-configuration/. I applied the fix he suggested but unfortunately that didn’t work :(. He also mentioned that it worked in an MVC application (this one was a WebForm application) so I tried creating a simple MVC 4 application and guess what, it worked there as Sandrino said :).
For now, I’m happy with what I’ve got and will focus on building some applications consuming ACS and see what this service has to offer.
Alternative Approach
While working on this, I realized an alternative approach to get up and running with ACS. Here’s what you would need to do:
- Create a new Access Control Service in Windows Azure Portal.
- Once the service is active, click on Manage button to manage that service. You will be taken to the ACS portal for your service.
- Configure Identity Providers.
- Get the management key from “Management service” section.
- Head back to Visual Studio project and configure ACS. You would need the name of the service and the management key.
- The tooling in Visual Studio takes care of creating “Relaying party applications” for you based on your project settings.
Summary
I spent considerable amount of time setting up this thing which kind of frustrated me. I hope this post will save you some time and frustration. Also this is the first time I looked at this service so it is highly likely I may have made some mistakes or included them here based on my sheer ignorance. Please feel free to correct me if I have provided incorrect information.
Happy Coding!!!